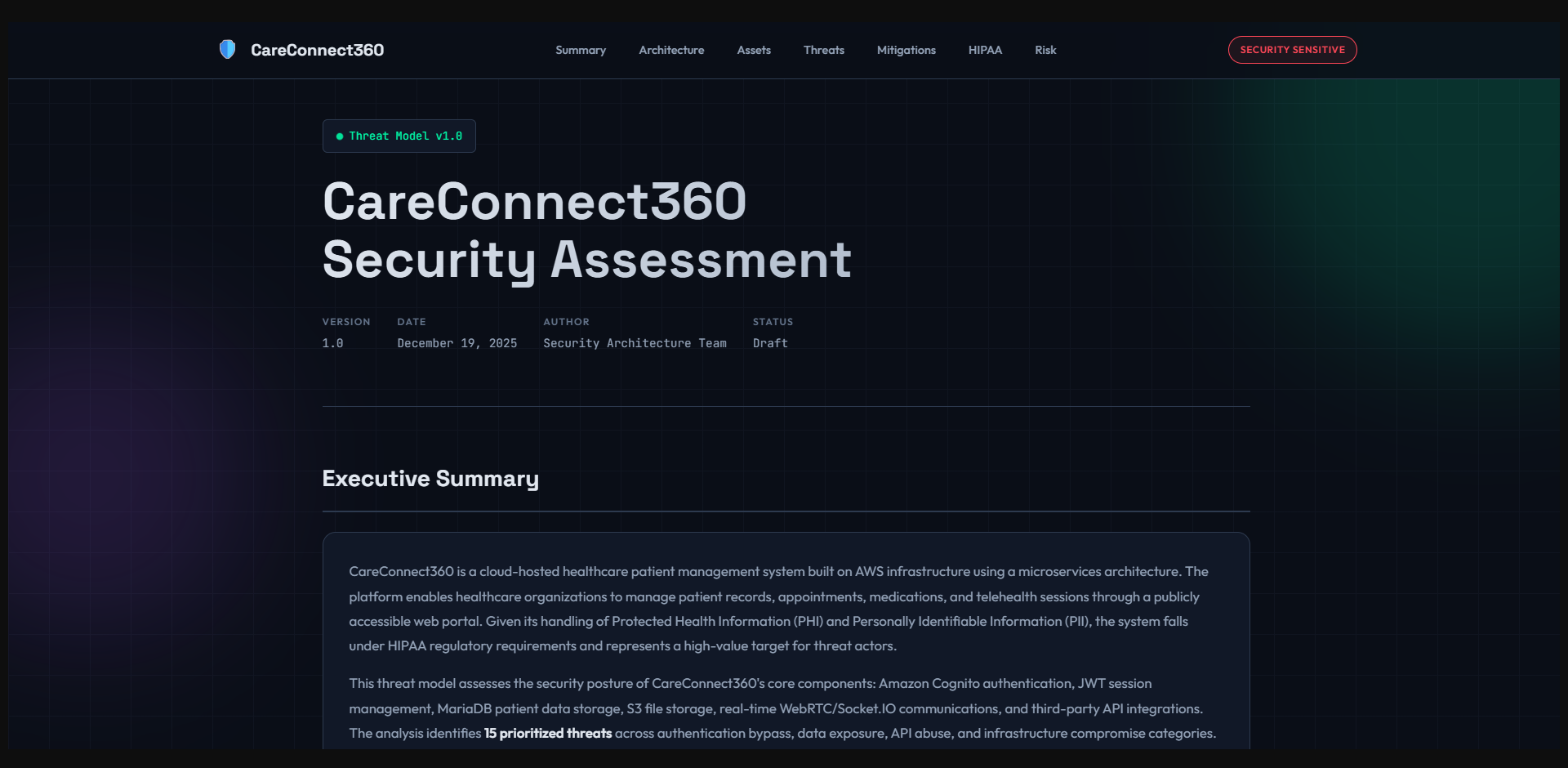
End-to-End DevSecOps Pipeline with SIEM Integration
Production-grade security automation across the entire software delivery lifecycle with threat detection streamed to Splunk.
- Challenge
- Security scanning typically happens too late — after deployment, after the vulnerability is already live. And when threats are detected at runtime, findings sit in separate consoles.
- Solution
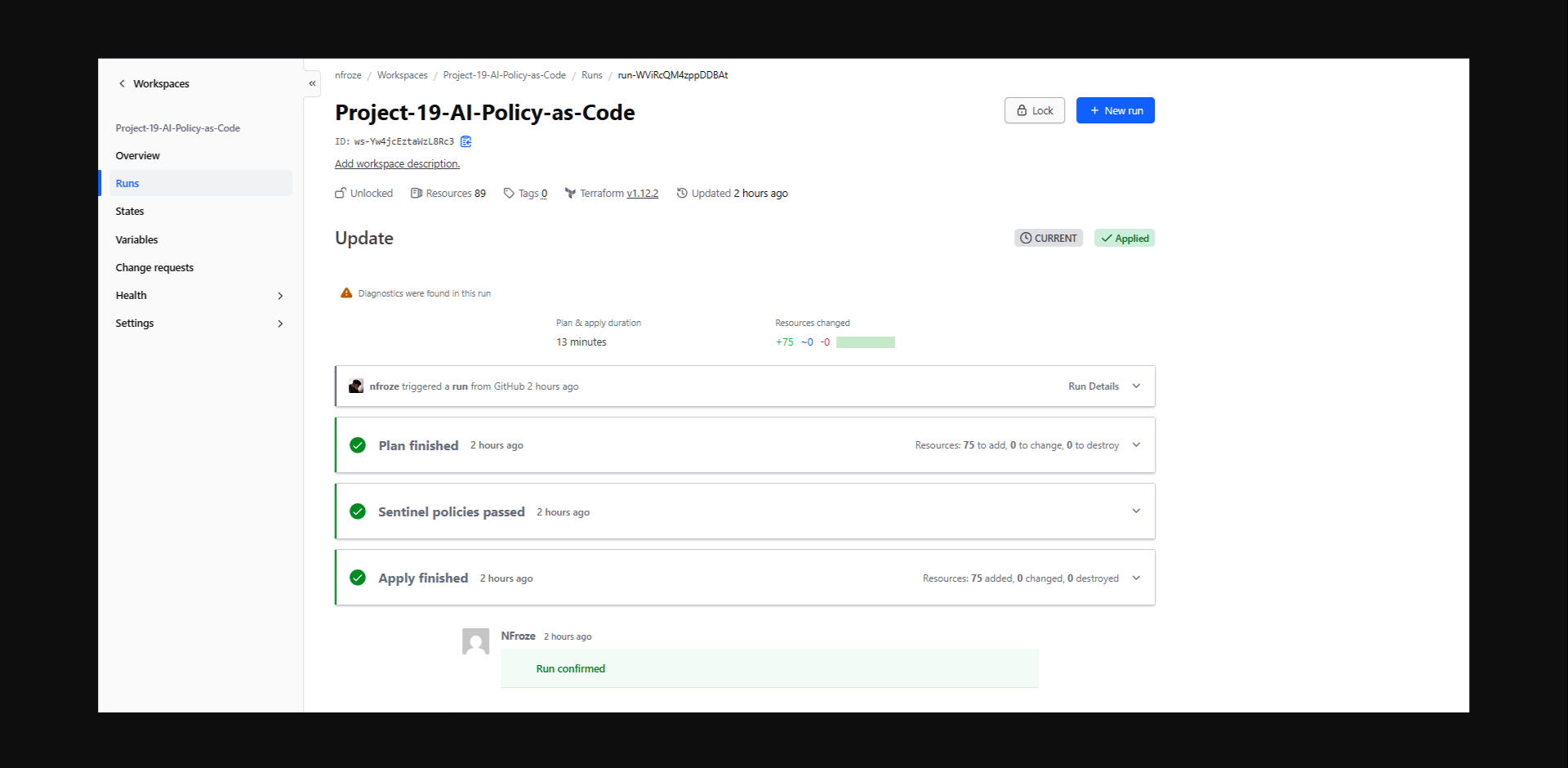
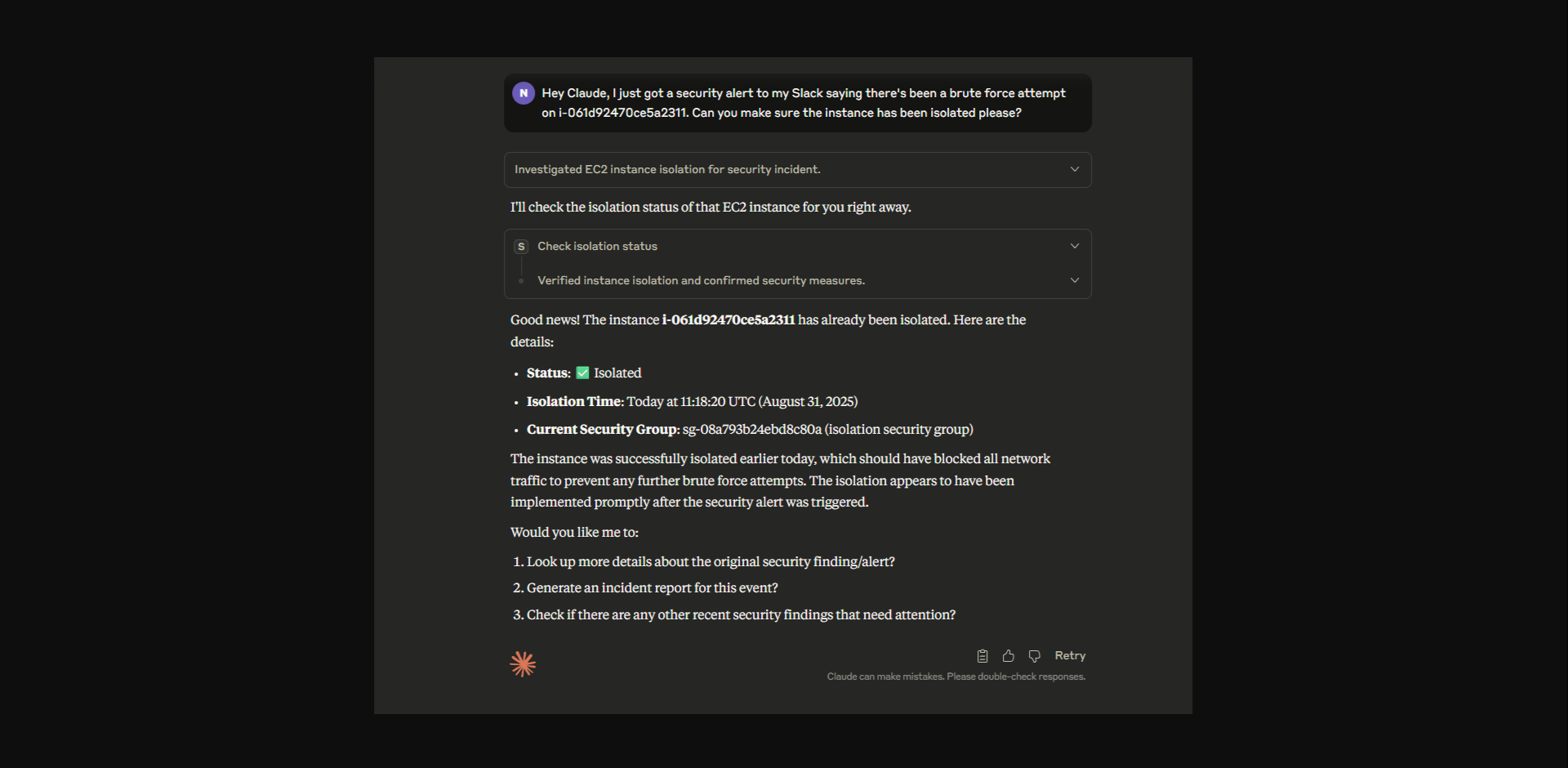
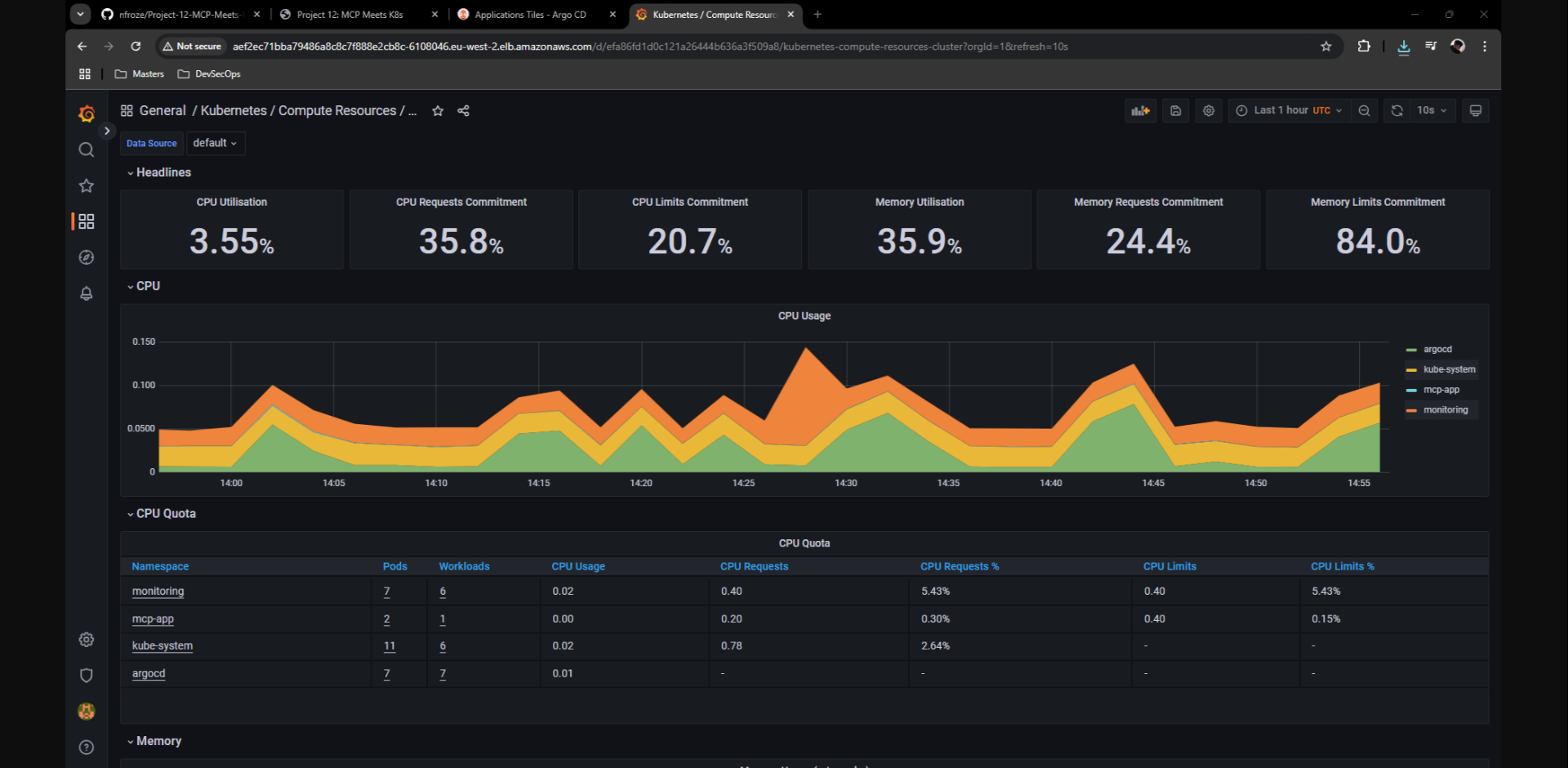
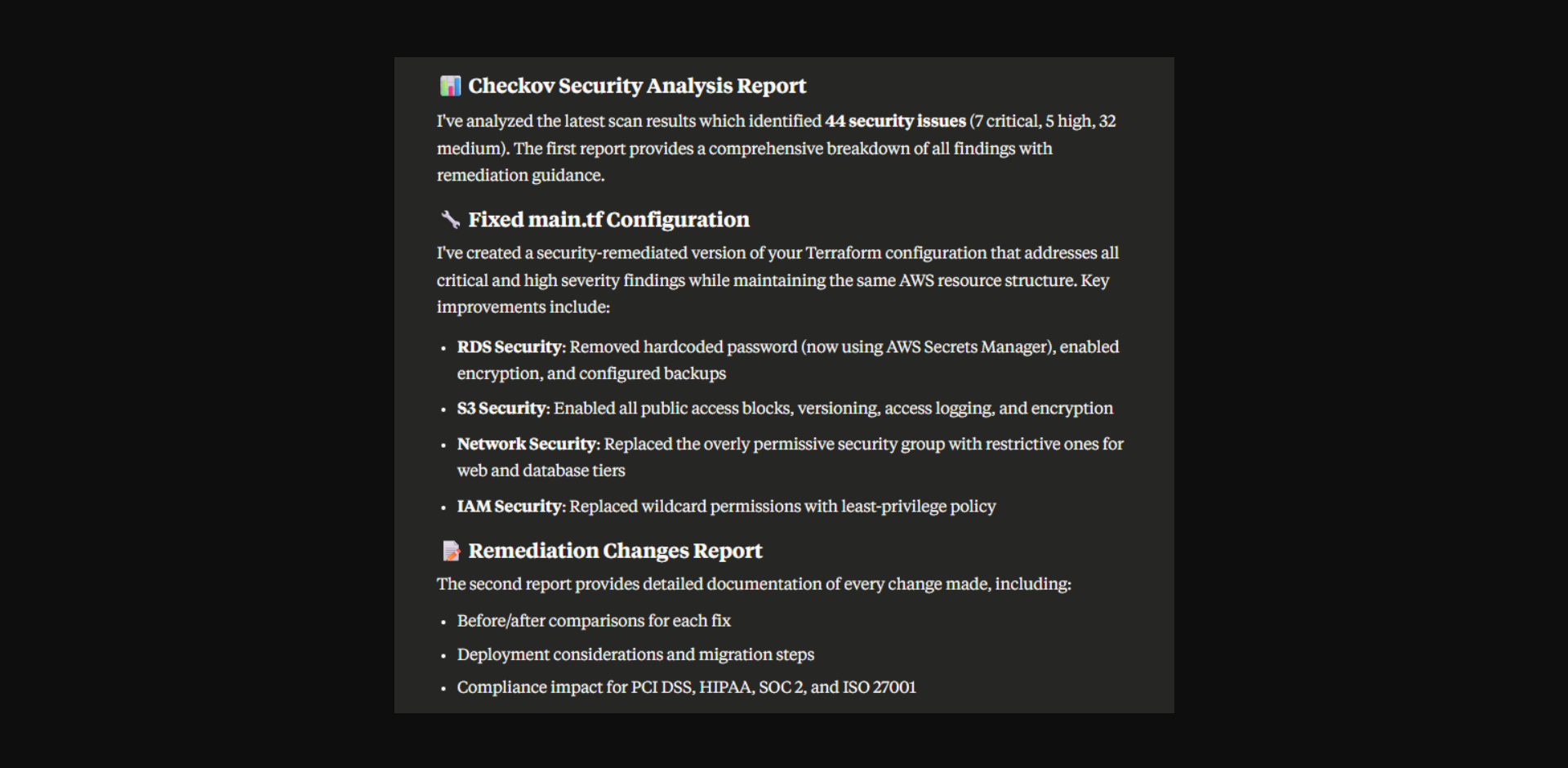
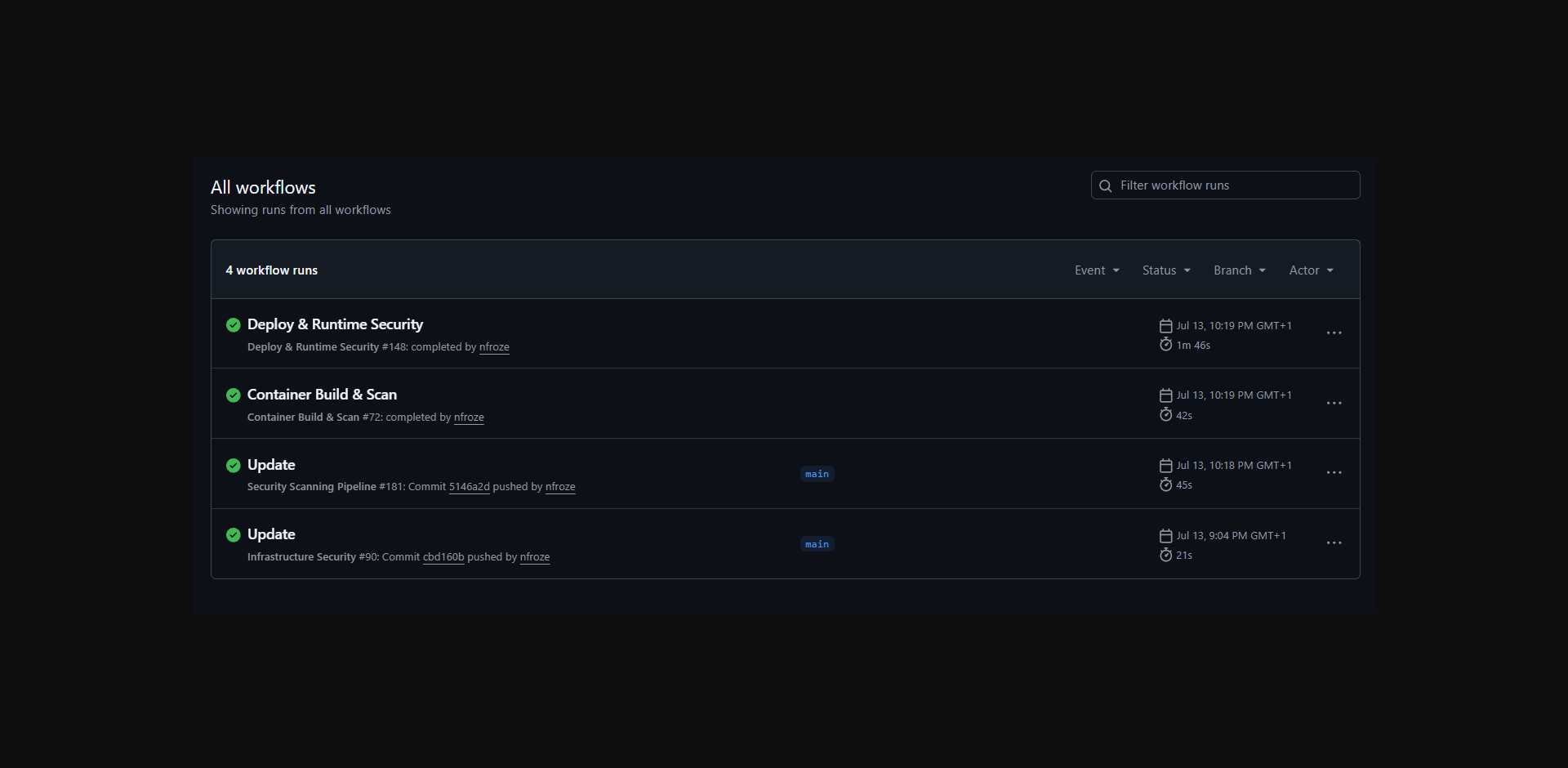
- Four-stage pipeline with Semgrep SAST, Trivy SCA, Gitleaks secrets detection, and Checkov IaC scanning. Security gates block non-compliant code. GuardDuty findings and CloudWatch logs stream via Lambda to Splunk Cloud. Hardened Kubernetes manifests: non-root containers, read-only filesystem, all capabilities dropped.
- Outcome
- Shift-left security with runtime visibility — vulnerabilities caught at commit, threats detected in production visible in SIEM.